Echo Chambers Are the New Attack Surface: How Social Engineering Evolved in 2026
The most significant shift in cybersecurity isn’t a new exploit or zero-day vulnerability. It’s the weaponization of the information environments where your employees already live—and new research reveals why traditional security training isn’t enough.
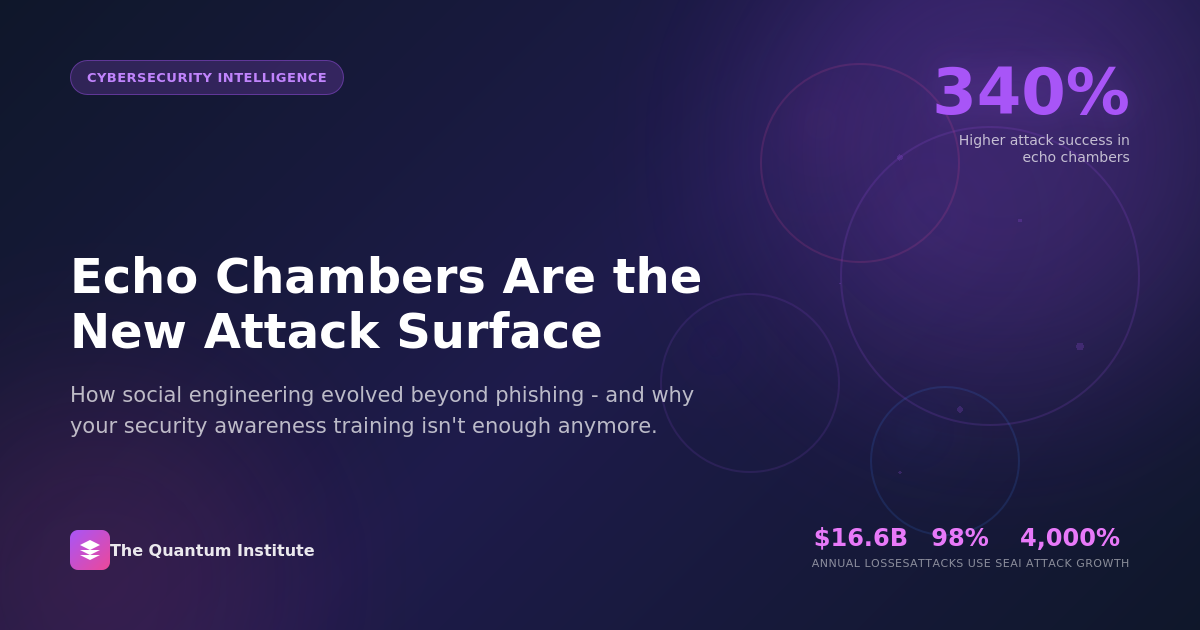
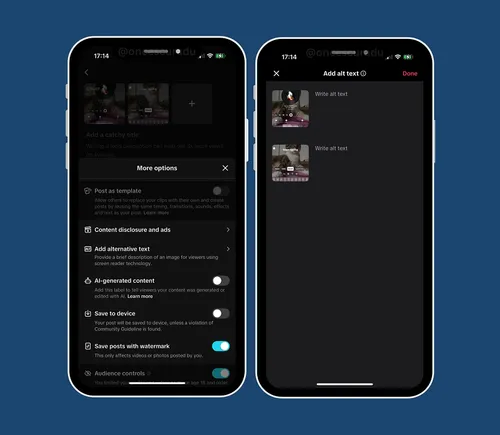
Social engineering remains the dominant attack vector, but its economics have fundamentally shifted. Research published in Social Engineering Attack Vectors: Trends and Prevention Techniques 2026 from The Quantum Institute documents several inflection points: But the most striking finding isn’t about scale—it’s about method. Stolen credentials (16%) have now surpassed traditional phishing (14%) as the primary initial access vector. The implications are significant: attackers have learned that compromising human judgment yields better returns than compromising systems. The research introduces what may be the most important concept in corporate security literature this year: echo chamber weaponization. Social media algorithms create ideologically homogeneous information environments—“filter bubbles” where users encounter primarily content that reinforces existing beliefs. What began as a platform engagement optimization has become a security liability. The data is stark: social engineering attacks achieve 340% higher success rates when campaigns target individuals within ideologically aligned echo chambers. The psychological mechanisms are well-documented: Confirmation Bias Amplification Targets within echo chambers are predisposed to accept information that aligns with group consensus. Attackers craft pretexts that fit existing narratives, dramatically reducing skepticism. Group Polarization Effects Echo chambers normalize increasingly extreme positions, making urgent or unusual requests seem more plausible when framed within group context. Reduced Critical Evaluation Continuous exposure to aligned content atrophies critical evaluation skills. The research terms this “cognitive diversity collapse”—the gradual loss of ability to evaluate information from outside one’s information environment. Authority Amplification Within closed communities, perceived authorities carry disproportionate influence. Attackers impersonating or compromising community leaders achieve success rates far exceeding traditional impersonation attacks. The research documents a fundamental transformation: artificial intelligence has converted social engineering from an art practiced by skilled individuals into a science executed at industrial scale. Key AI-enabled capabilities now in active use: The research documents cases where AI-generated voice clones successfully authorized wire transfers exceeding $10 million. In one instance, a deepfake video call convinced a finance employee to transfer $25 million to attacker-controlled accounts. The 4,000% increase in AI-powered attacks documented in the research reflects not just growth in volume, but growth in effectiveness. Attack success rates have improved even as awareness has increased. The research moves beyond threat documentation to analyze defensive measures with proven effectiveness. Key findings on investment ROI: Security Awareness Training Organizations with mature training programs report 70% reduction in successful social engineering attacks. However, the research emphasizes that traditional annual compliance training shows minimal impact—effective programs require continuous reinforcement and simulated attack exercises. Multi-Factor Authentication Properly implemented MFA reduces account compromise by 99.9%. The research notes that SMS-based MFA provides substantially less protection than authenticator apps or hardware tokens, and that MFA fatigue attacks are increasing. AI-Powered Detection Organizations deploying AI-based email security report $3.05 million average savings per prevented breach. The research identifies specific capabilities that drive outcomes: behavioral analysis, communication pattern deviation detection, and real-time sender verification. Cognitive Diversity Programs A novel finding: organizations implementing “information diet auditing” and encouraging employees to engage with diverse information sources show measurably improved resistance to echo chamber exploitation. This represents an emerging best practice not yet widely adopted. The research provides a prioritized implementation roadmap for organizations seeking to strengthen defenses: Days 1-30: Foundation - Deploy MFA across all systems (prioritize hardware tokens for high-risk roles) - Implement AI-powered email security - Establish baseline metrics for social engineering attempt detection - Conduct initial workforce vulnerability assessment Days 31-60: Capability Building - Launch continuous security awareness program - Deploy endpoint detection focused on credential theft - Implement communication channel verification protocols - Establish executive impersonation monitoring Days 61-90: Maturity - Conduct simulated social engineering exercises - Implement cognitive diversity initiatives - Establish cross-functional incident response protocols - Deploy advanced threat intelligence integration The research provides detailed analysis across industries, noting that attack sophistication and targeting varies significantly: Financial Services face the highest-value targeting, with average demanded ransoms 3x higher than cross-industry averages. Business email compromise (BEC) attacks specifically targeting wire transfers remain the primary threat vector. Healthcare organizations face unique vulnerabilities around patient data access urgency. Attackers exploit clinical workflows where speed often takes precedence over verification. Manufacturing sees increasing operational technology (OT) targeting, with social engineering used to establish initial access before pivoting to industrial control systems. Professional Services face supply chain social engineering, with attackers using compromised firms as vectors into client organizations. The research frames social engineering as a board-level risk requiring governance attention beyond traditional IT security oversight. Recommended board reporting metrics include: Organizations treating social engineering as purely a technical problem are systematically underinvesting in the human factors that determine outcomes. Comprehensive attack vector analysis, sector-specific guidance, and implementation frameworks are available in Social Engineering Attack Vectors: Trends and Prevention Techniques 2026 from The Quantum Institute. Word count: 1,087 About The Quantum Institute: The Quantum Institute is a strategic intelligence research firm providing cybersecurity analysis and emerging technology risk assessment to Fortune 500 corporations, government agencies, and institutional investors.  The most significant shift in cybersecurity isn’t a new exploit or zero-day vulnerability. It’s the weaponization of the information environments where your employees already live—and new research reveals why traditional security training isn’t enough.
The most significant shift in cybersecurity isn’t a new exploit or zero-day vulnerability. It’s the weaponization of the information environments where your employees already live—and new research reveals why traditional security training isn’t enough.The Numbers That Changed Everything
The Echo Chamber Vulnerability
AI Has Industrialized the Threat
What’s Actually Working
The 90-Day Implementation Framework
Sector-Specific Considerations
The Board-Level Conversation

 MikeTyes
MikeTyes